Applied Sciences | Free Full-Text | VPNFilter Malware Analysis on Cyber Threat in Smart Home Network

TP-Link - Connect with TP-Link, Connect RELIABLY SMART. #S O C I A L D I S T A N C I N G #stayhome #staysecure #stayapart #stayconnected #reliablysmart | Facebook

NETGEAR RAX10 - wireless router - Wi-Fi 6 - Wi-Fi 6 - desktop - RAX10-100NAS - Wireless Routers - CDW.com

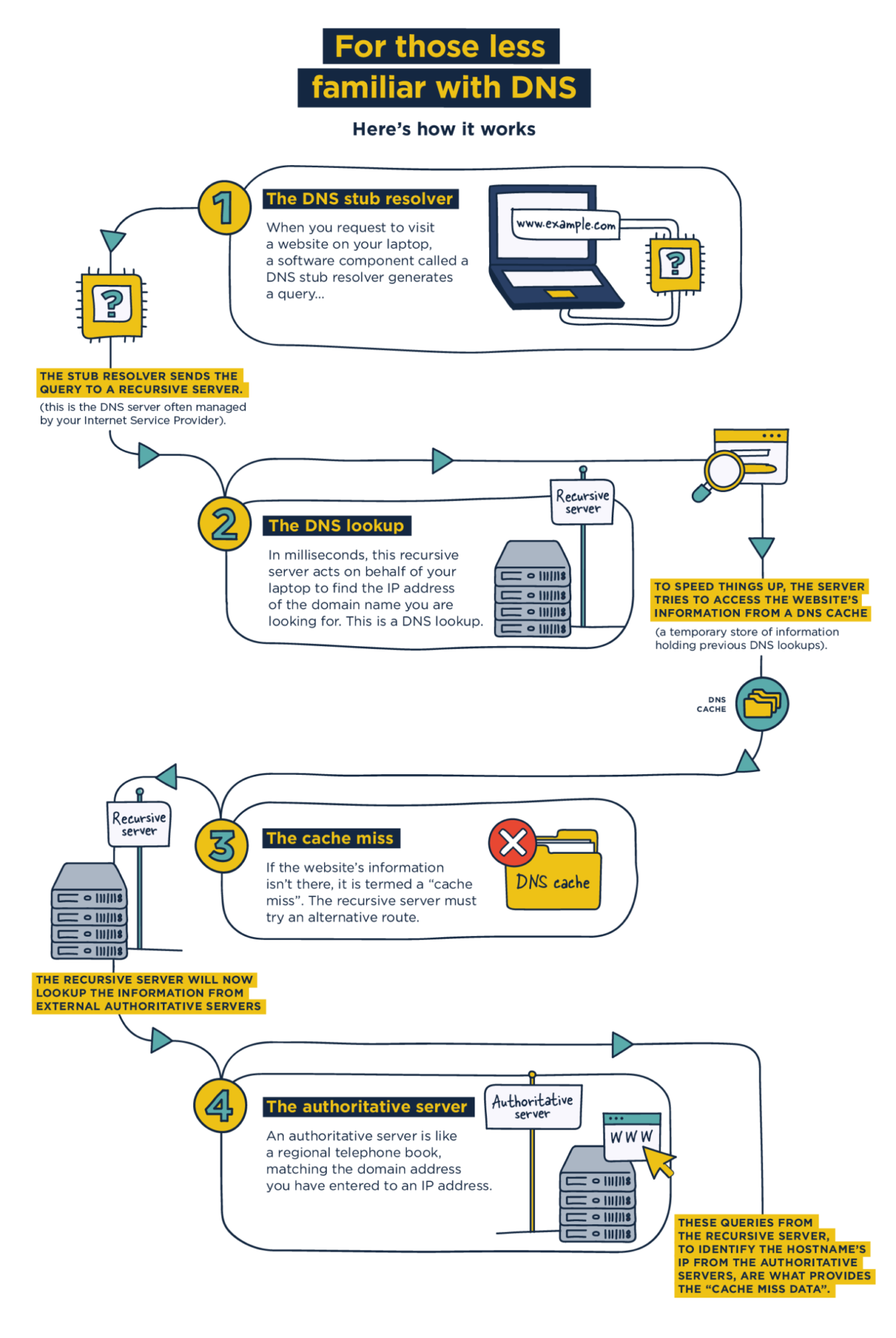
a) Standard configuration: the router acts as a proxy for DNS queries,... | Download Scientific Diagram

In Exp. 1 a client queries a recursive resolver, and the communication... | Download Scientific Diagram
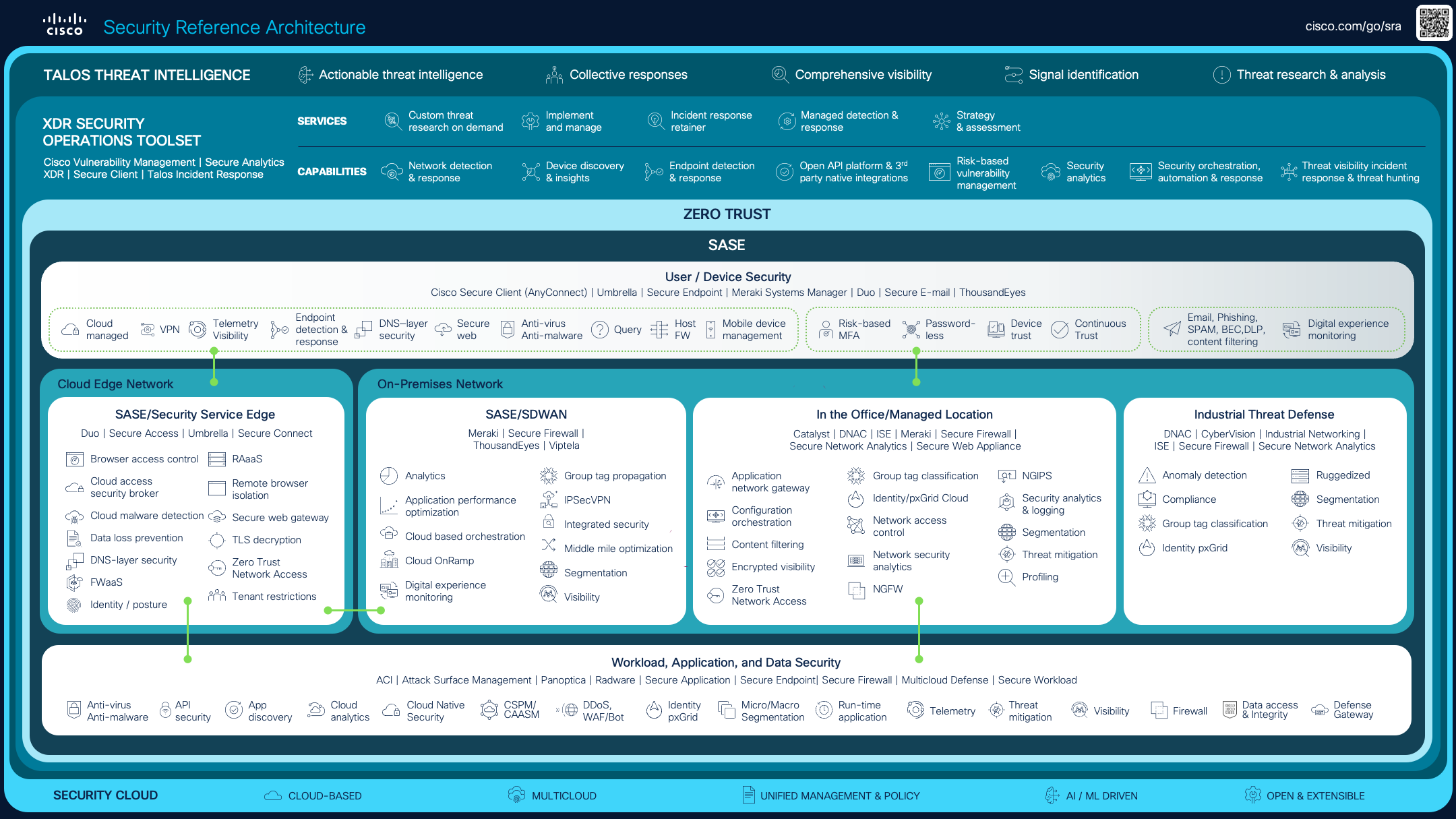
Electronics | Free Full-Text | Real-Time Detection System for Data Exfiltration over DNS Tunneling Using Machine Learning

![How to remove Search.queryrouter.com [Chrome, Firefox, IE, Edge] How to remove Search.queryrouter.com [Chrome, Firefox, IE, Edge]](https://www.myantispyware.com/wp-content/uploads/2016/12/search.queryrouter.com_search_results.jpg)